
Happy new year! (and make sure you stay away from Cerber)
As 2016 came to an end, we have to thank you […]

As 2016 came to an end, we have to thank you […]

Ransomware developers have always been competitive, trying to get more […]

Holiday shopping this year is and will be more dangerous […]
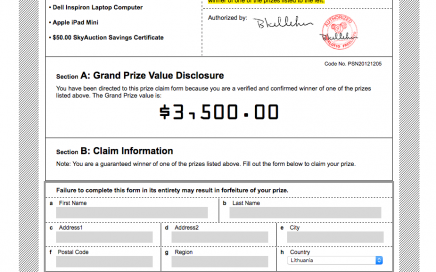
Most of the time we became excited when we hear […]

Ransomware and browser hijackers — a couple of this year’s […]
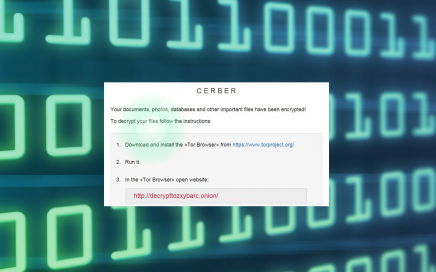
We have been hearing news about Cerber ransomware for more […]

Patching and updating – these are the primary keys towards […]

It seems that cyber criminals have advanced to the new […]

Ransomware viruses have been around for years, just recently, though, […]

After several years, Yahoo reports about a huge data breach that […]
Several weeks ago, researchers from one of eSolutions projects, 2-spyware, received a […]
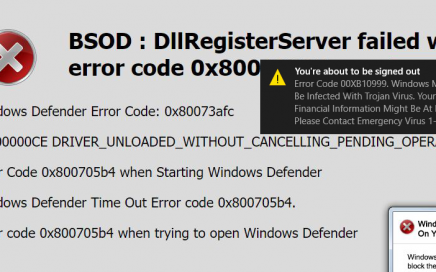
People hate Blue Screen of Death (BSOD) error because it can force their computers […]

Nowadays, Internet users are facing threats every minute they spend […]
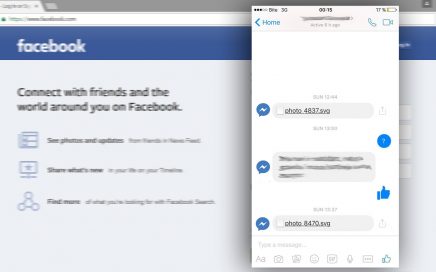
Facebook has the audience of more than 750 million users, […]
It hasn’t been a week since eSolutions team has announced […]
As the extensive globalization continues to unify the world, most […]