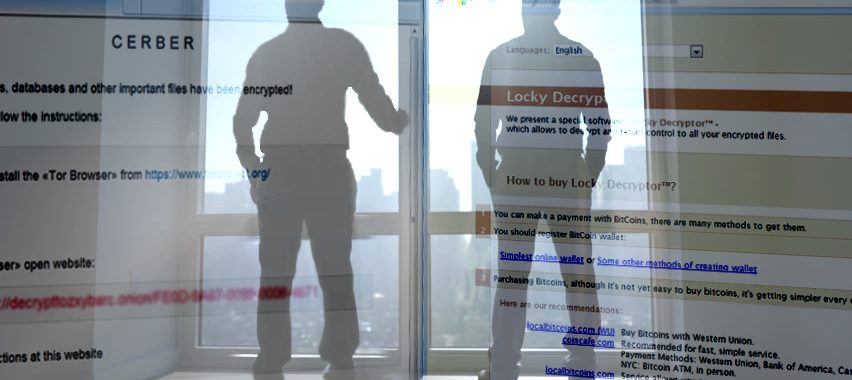
Cerber or Locky – ever-evolving and ever-lasting cyber issues
In case you started wondering whether, by any chance, the notorious two ransomware giants got finally terminated, we are sorry to disappoint you. It seems that the developers of these two threats have wisely spent the summer time: improved viruses target netizens again. What’s new and what should you beware of?
Cerber now sniffs for personal data
Corresponding to its original name – the mythical creature Cerber – the developers decided to add data-stealing features. Now the latest version of the virus, which is distributed as CRBR Encryptor, is able to capture browser passwords and bitcoin wallet-related information.
Besides looking for Chrome, Internet Explorer, Firefox and other browser passcodes, the infection also attempts to steal Bitcoin Core wallet, Multibit and Electrum wallet information.
IT specialists suspect that the source code enabling the mentioned function might belong to another project. Though this new update certainly makes the malware even more menacing, data stealing ransomware is not a novelty. Last year some CryptXXX variants were spotted in engaging in data stealing activity as well.
Locky strikes again in a new disguise
While the title of “Locky ransomware” had been regularly flickering in the media headlines last year, its authors has not abandoned this project. In fact, the time periods between each version imply that the crooks have been working on the new more destructive techniques. Consequently, this summer they decided to drop the habit of naming their virus versions after the names of Egyptian and Scandinavian deities and return to the European mythology.
IT specialists have caught its new version – Diablo6 ransomware – spreading via a new malicious spam campaign. However, observing the tendency, Locky developers have not mastered any extraordinary new technique. As in previous cases, they test targeted users’ curiosity. The compromised email might be sent from an unknown sender with a brief message content: “Files attached. Thanks”
Opening the E [date] (random_numer).docx file will executes VBS downloader script which then downloads the main payload of the virus. During the encryption process, the malware will append ridiculously long [first_8_hexadecimal_chars_of_id]-[next_4_hexadecimal_chars_of_id]-[next_4_hexadecimal_chars_of_id]-[4_hexadecimal_chars]-[12_hexadecimal_chars].diablo6 file extension. The current version is relatively modest—it only asks for .49 bitcoin amounting $1.600.
Unfortunately, neither of the ransomware threats are decryptable at the moment. While cyber security specialists continue working on the countermeasures, the virtual community should arm up with awareness and knowledge. Except Cerber, which indeed keeps evolving at the alarming rate, Locky developers seem to rely on the same spam campaigns. If you manage to bridle your curiosity and treat incoming spam emails with cautiousness, you will lower the risk of encountering file-encrypting threats.